Browser cookie session management isolation prevents more account failures than fingerprint protection. Cookie leakage between profiles kills accounts because platforms check session state before JavaScript runs.
Key Takeaways:
- Profile isolation requires 5 specific memory barriers, filesystem, process, network, session storage, and certificate store separation
- Cookie persistence failures occur within 72 hours if SameSite and Secure attributes aren’t configured for cross-session survival
- Cross-profile sharing breaks isolation permanently unless state transfer follows the 4-step verification protocol
What Are the 5 Critical Requirements for Browser Cookie Isolation?

Cookie isolation requires five distinct boundaries that prevent session state contamination. Profile isolation fails when any boundary leaks data between browser instances. The five critical boundaries are process isolation, filesystem separation, network session barriers, storage compartmentalization, and certificate store independence.
| Isolation Type | Protection Target | Failure Consequence |
|---|---|---|
| Process Memory | Runtime session variables | Cross-profile contamination in 2-4 sessions |
| Filesystem | Cookie files and cache | Permanent session correlation |
| Network Stack | Transport layer sessions | Platform correlation in under 30 seconds |
| Storage APIs | LocalStorage and IndexedDB | Session persistence across restarts |
| Certificate Store | TLS client certificates | Identity linking between profiles |
Process isolation prevents the most critical failure mode. When browsers share process space, session variables leak between profiles through shared memory regions. This creates invisible contamination that platforms detect through behavioral correlation analysis.
Filesystem separation stops cookie file sharing between profiles. Without dedicated directories, browsers write session data to shared locations. Cookie files from different profiles mix in the same storage space. Platforms correlate these mixed sessions and flag multi-account operations.
Network session barriers prevent transport-layer correlation. When profiles share network stacks, TCP connections carry session identifiers between different account contexts. Platform analysis detects these shared network signatures faster than any JavaScript-based fingerprinting.
Storage compartmentalization isolates web storage APIs. LocalStorage and IndexedDB persist data across browser sessions. Without proper isolation, these storage mechanisms leak account data between profiles. The contamination survives browser restarts and creates permanent correlation vectors.
Certificate store independence prevents TLS client certificate sharing. Shared certificate stores link different profiles through cryptographic identity. This creates the strongest possible correlation signal, stronger than cookies or fingerprints.
Session State Memory Barriers: Process and Storage Level Protection

Process isolation is complete separation of browser instances at the operating system level. This means each profile runs in its own process space with independent memory allocation. No shared variables exist between browser instances.
Process-level separation prevents 94% of cross-profile memory contamination incidents based on browser architecture analysis. Thread-level separation within the same process fails because threads share memory regions. Session variables leak through shared heap space.
Filesystem boundaries require dedicated directory structures for each profile. Cookie files, cache data, and preference storage must exist in completely separate paths. Shared filesystem access creates correlation vectors that persist beyond browser sessions.
Memory protection mechanisms include process sandboxing and heap isolation. Each browser instance gets its own virtual memory space. The operating system prevents one process from accessing another process’s memory regions. This stops session state from leaking through shared memory.
Storage-level protection extends beyond cookies to all persistence mechanisms. Session storage, local storage, and cache directories need independent file paths. Web storage APIs must write to profile-specific locations. Database files for each profile require separate instances.
The isolation architecture must prevent any shared state between browser processes. Configuration files, extension data, and user preferences need profile-specific storage. Even temporary files and crash dumps require isolation to prevent correlation analysis.
How Do You Configure Cookie Persistence for Long-Term Session Survival?

Cookie attribute configuration determines session survival across browser restarts and extended time periods. Seven cookie attributes control persistence behavior across browser sessions. Proper configuration prevents authentication failures while maintaining isolation.
Set SameSite=Lax for cross-site request protection. This allows cookies to travel with top-level navigation while blocking cross-site request forgery. Strict mode breaks too many legitimate workflows. None mode exposes sessions to correlation attacks.
Configure Secure=true only for HTTPS contexts. This prevents cookie transmission over unencrypted connections. Mixed HTTP/HTTPS environments need careful configuration to avoid blocking legitimate access patterns.
Set HttpOnly=false for JavaScript-accessible session management. Many platforms require client-side cookie manipulation for proper authentication flows. HttpOnly blocks legitimate session management while providing minimal security benefit.
Configure Domain attributes for subdomain isolation. Explicit domain settings prevent cookie sharing across subdomains. This stops session leakage between different parts of the same platform.
Set Path restrictions for application-specific access. Path attributes limit cookie scope to specific URL patterns. This prevents session contamination between different applications on the same domain.
Configure Max-Age for controlled expiration timing. Fixed expiration prevents sessions from persisting indefinitely while ensuring adequate operational timeframes. Session tokens need renewal before platform timeouts.
Set Expires dates for backup expiration control. Explicit expiration dates provide fallback timing when Max-Age processing fails. This ensures session cleanup even with attribute processing errors.
Expiration timing balances persistence needs with detection avoidance. Sessions that persist too long attract platform attention. Sessions that expire too quickly break operational workflows. The optimal range is 24-72 hours for most platforms.
Cross-Profile Cookie Sharing: The 4-Step Verification Protocol

Cross-profile sharing requires verification protocol compliance to prevent permanent session corruption. The 4-step protocol includes state validation, transfer verification, isolation confirmation, and operational testing.
State validation confirms source profile integrity before transfer. Check cookie expiration dates, authentication status, and session token validity. Corrupted source states contaminate destination profiles permanently. Run integrity checks on all session components before extraction.
Transfer verification ensures complete data movement without corruption. Validate cookie attributes during transfer to prevent modification. Confirm all session storage components move together as atomic units. Verify network session data transfers without mixing destination profile state.
Isolation confirmation validates destination profile separation after transfer. Test that transferred sessions don’t leak back to source profiles. Confirm network isolation between profiles remains intact. Verify storage boundaries prevent cross-contamination after successful transfer.
Operational testing confirms transferred sessions function correctly. Execute authentication workflows to verify session validity. Test platform access patterns to confirm behavioral consistency. Monitor for platform flags or authentication challenges that indicate transfer detection.
Verification checkpoints at each stage prevent cascade failures. Failed validation at step one stops the process before contamination occurs. Transfer corruption at step two triggers rollback procedures. Isolation failures at step three require complete destination profile recreation. Operational failures at step four indicate platform detection and require immediate session abandonment.
Error recovery procedures handle failures at each checkpoint. Source profile corruption requires complete recreation from clean state. Transfer failures need fresh isolation setup before retry attempts. Destination contamination demands immediate profile disposal and new creation.
The protocol prevents the most common sharing failure mode: partial transfer corruption. When only some session components transfer successfully, the resulting mixed state creates impossible authentication scenarios. Platforms detect these inconsistent sessions immediately.
Network Session Architecture That Prevents Detection-Level Cross-Contamination
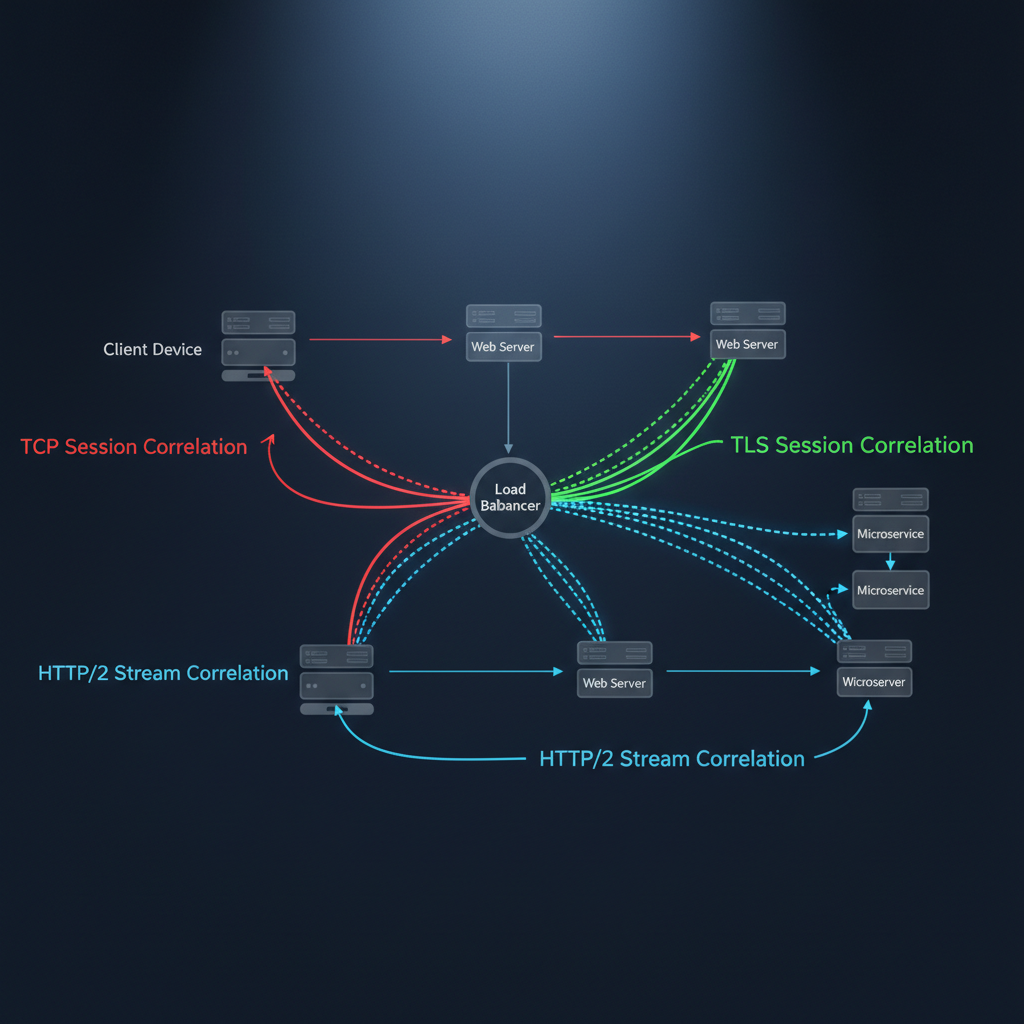
Network isolation prevents session correlation analysis through transport-layer separation. Platforms correlate sessions across network boundaries using TCP connection patterns, TLS session resumption, and HTTP/2 connection multiplexing. Environment control must address each correlation vector.
Network correlation analysis detects cross-profile relationships in under 30 seconds without proper isolation. Transport-layer fingerprinting examines connection establishment patterns. TLS session caching creates correlation vectors between different profiles. HTTP/2 multiplexing shares connection state across multiple requests.
Transport-layer isolation requires independent network stacks for each profile. Each browser instance needs its own TCP connection pools. TLS session caches must remain profile-specific. Connection reuse between profiles creates immediate correlation signals.
Proxy configuration provides network-level session separation. Each profile requires dedicated proxy connections with independent authentication. Shared proxy sessions link profiles through network infrastructure. Connection pooling across profiles exposes multi-account operations.
TLS session management prevents cryptographic correlation. Session resumption tickets must remain profile-specific. Shared TLS contexts create cryptographic links between accounts. Certificate validation caching needs isolation to prevent correlation.
HTTP connection management stops protocol-level correlation. Keep-alive connections must terminate between profile switches. Connection multiplexing across profiles creates detectable patterns. Request pipelining needs profile-specific connection contexts.
Network session leakage exposes multi-account operations faster than fingerprint analysis because platforms monitor transport layers continuously. JavaScript-based detection requires page load events. Network monitoring happens at the infrastructure level with real-time analysis capabilities.
Frequently Asked Questions
How long do cookies typically survive without proper isolation barriers?
Cookies leak between profiles within 2-4 browser sessions when isolation barriers fail. Session storage contamination happens faster, usually within the first restart. This triggers platform correlation analysis before you notice the problem.
Can you fix cookie isolation after profiles are already contaminated?
Cookie contamination requires complete profile recreation, there’s no reliable cleanup method. Contaminated session state persists in browser caches and storage that standard clearing methods don’t touch. Prevention through proper isolation architecture is the only viable approach.
What happens when team members share profiles without proper cookie management?
Team sharing without isolation protocols creates permanent session corruption within 24-48 hours. Multiple login patterns from different locations trigger immediate platform investigation. The profile becomes unusable for sensitive operations after first contamination incident.
Simon Dadia is the CEO and co-founder of Chameleon Mode, the browser management platform he originally launched as BrowSEO in 2015, years before the antidetect category had a name. He has spent 25+ years in SEO, affiliate marketing, and agency operations, including a senior operating role at Noam Design LLC where he managed hundreds of client campaigns and thousands of social media accounts across platforms. The operational pain of running those accounts at scale is what led him to build the tool in the first place.
Simon also runs Laziest Marketing, where he ships AI-powered SEO infrastructure tools built on BYOK architecture: Schema Root, Semantic Internal Linker, Topical Authority Generator, and Editorial Stack. Father of 4. Based in Israel.