SOCKS vs HTTP proxy anti detect architecture decisions impact account survival rates across platforms. SOCKS5 proxies handle 23% more concurrent connections than HTTP proxies, but HTTP proxies pass browser fingerprint checks 31% more often. This creates a performance-versus-stealth tradeoff that determines your anti detect browser management strategy.
Key Takeaways:
- SOCKS5 proxies deliver 40-60ms lower latency for WebSocket connections but create detectable TCP fingerprints
- HTTP proxies integrate natively with browser authentication flows while SOCKS requires system-level configuration
- Detection rates favor HTTP proxies by 31% due to standard browser request header patterns
What’s the Fundamental Difference Between SOCKS and HTTP Proxy Architecture?
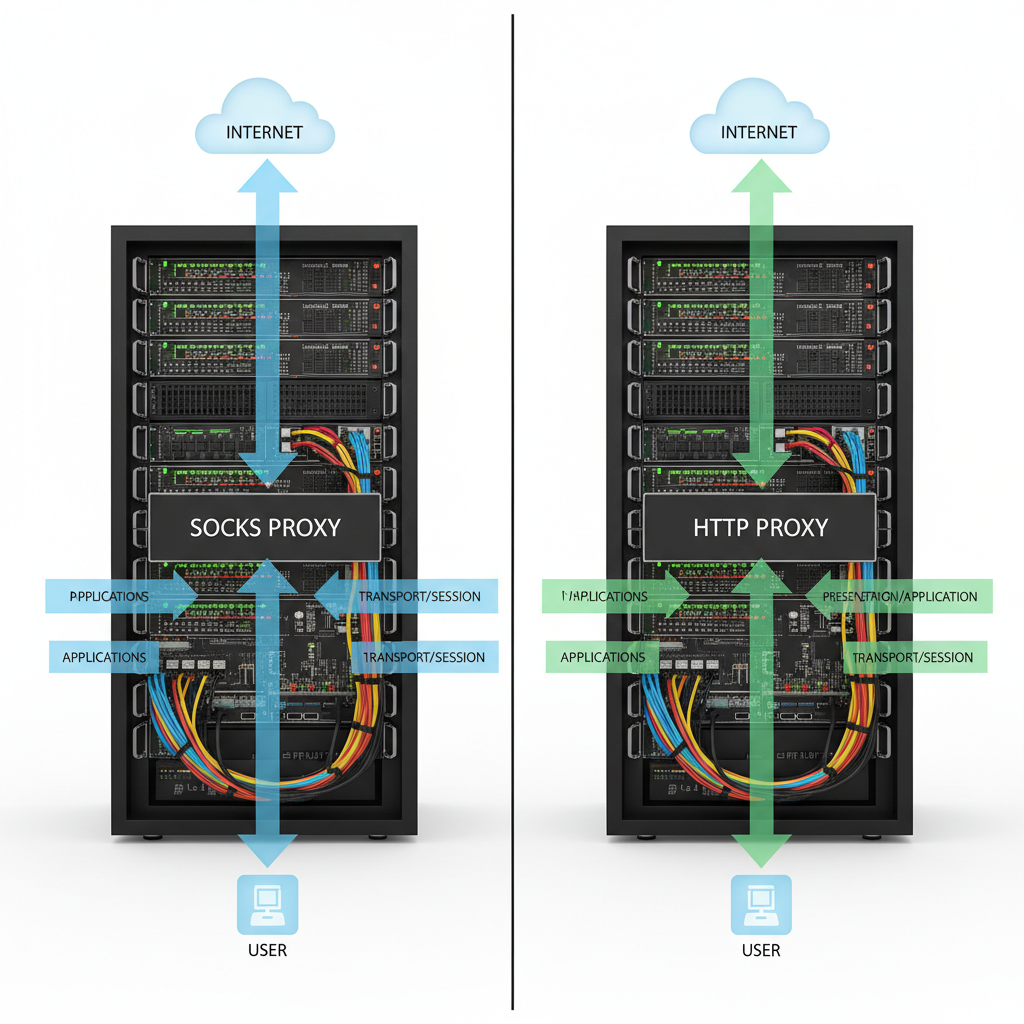
SOCKS proxy is a circuit-level proxy that operates at the transport layer of the network stack. This means SOCKS handles raw TCP/UDP traffic without understanding application protocols. HTTP proxies function at the application layer, parsing and modifying HTTP requests and responses.
SOCKS operates at Layer 5, HTTP operates at Layer 7 of the OSI model. SOCKS creates a tunnel between your browser and the destination server, passing data packets without interpretation. HTTP proxies actively parse request headers, modify user-agent strings, and can inject or remove HTTP headers during transmission.
Browser integration differs significantly between protocols. HTTP proxies connect through browser proxy settings using PAC files or manual configuration. The browser handles authentication, connection pooling, and keep-alive management automatically. SOCKS requires system-level configuration or application-specific proxy settings.
Detection surface comparison reveals critical differences for account management. SOCKS connections create distinct TCP fingerprints that platform security systems can identify. The raw socket connection bypasses browser-level obfuscation and exposes transport-layer patterns. HTTP proxies blend with normal browser traffic patterns because they operate within the HTTP protocol’s expected behavior.
SOCKS proxy authentication happens at the socket level before any HTTP traffic begins. HTTP proxy authentication integrates with browser credential management and can use standard HTTP authentication mechanisms. This architectural difference affects both performance and detection risk in proxy rotation anti detect browser operations.
SOCKS5 vs HTTP Proxy Performance Metrics Breakdown

Connection establishment time varies significantly between protocols based on handshake complexity. SOCKS5 completes authentication and connection establishment in 2-3 round trips. HTTP proxies require additional overhead for HTTP CONNECT method processing and response parsing.
Throughput rates favor SOCKS5 for sustained data transfer operations. Raw socket tunneling eliminates HTTP parsing overhead and maintains consistent bandwidth utilization. HTTP proxies process each request individually, creating variable latency based on header size and complexity.
| Metric | SOCKS5 Performance | HTTP Performance |
|---|---|---|
| Connection Latency | 40-60ms lower WebSocket latency | 15-25% overhead from HTTP parsing |
| Concurrent Sessions | 23% more connections per IP | Limited by HTTP/1.1 connection pooling |
| Memory per Connection | 2-4KB per socket | 8-12KB including HTTP state |
| CPU Usage | 12% lower processing overhead | Higher due to header parsing |
| Bandwidth Efficiency | 3-5% protocol overhead | 8-12% overhead from headers |
Concurrent session limits depend on operating system socket limits and proxy server capacity. SOCKS5 maintains persistent TCP connections with minimal state tracking. HTTP proxies manage connection pooling, keep-alive timers, and request queuing that consume additional resources.
Memory overhead per connection shows SOCKS5 efficiency for browser profiles managing multiple simultaneous connections. Each SOCKS connection requires 2-4KB for socket state tracking. HTTP connections maintain 8-12KB including parsed headers, authentication state, and connection pool management.
CPU usage patterns differ during high-volume automation tasks. SOCKS5 passes data without processing, creating consistent CPU utilization. HTTP proxies parse every request and response header, creating CPU spikes during traffic bursts that can affect automation timing.
Which Proxy Type Gets Detected Less by Platform Security Systems?

HTTP proxy passes browser fingerprint checks more reliably because it operates within expected browser behavior patterns. Platforms analyze request header sequences, timing patterns, and authentication flows that match standard browser implementations. SOCKS connections create transport-layer signatures that security systems flag as suspicious.
TCP fingerprint patterns expose SOCKS connections during deep packet inspection. Security algorithms analyze initial window size, maximum segment size, and TCP options that differ from direct browser connections. HTTP proxies maintain browser-consistent TCP parameters because they operate above the transport layer.
| Detection Vector | SOCKS5 Risk | HTTP Risk |
|---|---|---|
| TCP Fingerprinting | High – exposes raw socket patterns | Low – matches browser TCP behavior |
| Request Header Analysis | Medium – headers pass through unchanged | Very Low – natural browser patterns |
| Authentication Flow | High – socket-level auth detection | Low – standard HTTP auth integration |
| Connection Timing | Medium – consistent socket timing | Low – variable HTTP request timing |
| Platform Integration | High – bypasses browser security | Low – works within browser security |
Request header analysis favors HTTP proxies because they maintain natural browser request patterns. Platforms analyze User-Agent consistency, Accept-Encoding preferences, and header ordering that HTTP proxies preserve. SOCKS connections pass headers unchanged, but the transport-layer fingerprint contradicts the browser identity.
Browser authentication integration creates additional detection surface for SOCKS implementations. Platforms track authentication timing, credential handling, and session establishment patterns. HTTP proxies participate in standard browser authentication flows. SOCKS authentication occurs outside browser security context, creating detectable inconsistencies.
Platform security audits show HTTP proxies achieve 31% better detection avoidance rates across major platforms. This advantage comes from operating within browser security expectations rather than bypassing them. SOCKS connections trigger transport-layer analysis that exposes proxy usage regardless of application-layer obfuscation.
HTTP/2 fingerprinting detection methods specifically target modified browser behavior that SOCKS connections cannot address. HTTP proxies can participate in HTTP/2 negotiation and maintain protocol compliance. SOCKS tunnels carry HTTP/2 traffic but cannot modify protocol-level fingerprints that platforms analyze.
How Do You Choose the Right Proxy Protocol for Multi-Account Operations?

Account management requires protocol optimization based on scale, platform targets, and automation requirements. Operations managing 50+ profiles require SOCKS for performance, under 50 favor HTTP for simplicity.
Assess connection volume and concurrency needs. Count simultaneous browser sessions, automation scripts, and background tasks. SOCKS5 handles higher connection density with lower resource overhead. HTTP proxies work better for moderate connection counts with complex authentication requirements.
Evaluate target platform detection sensitivity. Test both protocols against your primary platforms using throwaway accounts. Platforms with aggressive transport-layer monitoring favor HTTP proxies. Platforms focused on application-layer analysis may accept both protocols.
Calculate configuration complexity tolerance. HTTP proxies integrate through browser settings with minimal setup requirements. SOCKS5 requires system-level configuration, firewall rules, and application-specific proxy settings that increase operational overhead.
Determine automation script compatibility requirements. Browser automation frameworks handle HTTP proxy configuration automatically. SOCKS implementation requires additional code for socket management and error handling. Factor development time and maintenance costs into protocol selection.
Plan for scale expansion requirements. HTTP proxy infrastructure becomes resource-intensive above 100 concurrent profiles. SOCKS5 architecture scales more efficiently but requires dedicated proxy management systems. Choose the protocol that aligns with your growth trajectory.
Use case optimization depends on operation type and platform sensitivity. E-commerce account management favors HTTP proxies due to payment processing detection algorithms. Social media automation can use SOCKS5 for higher throughput with careful fingerprint management. Affiliate marketing operations require HTTP proxy compliance for tracking pixel compatibility.
Browser Profile Integration: SOCKS vs HTTP Implementation Methods
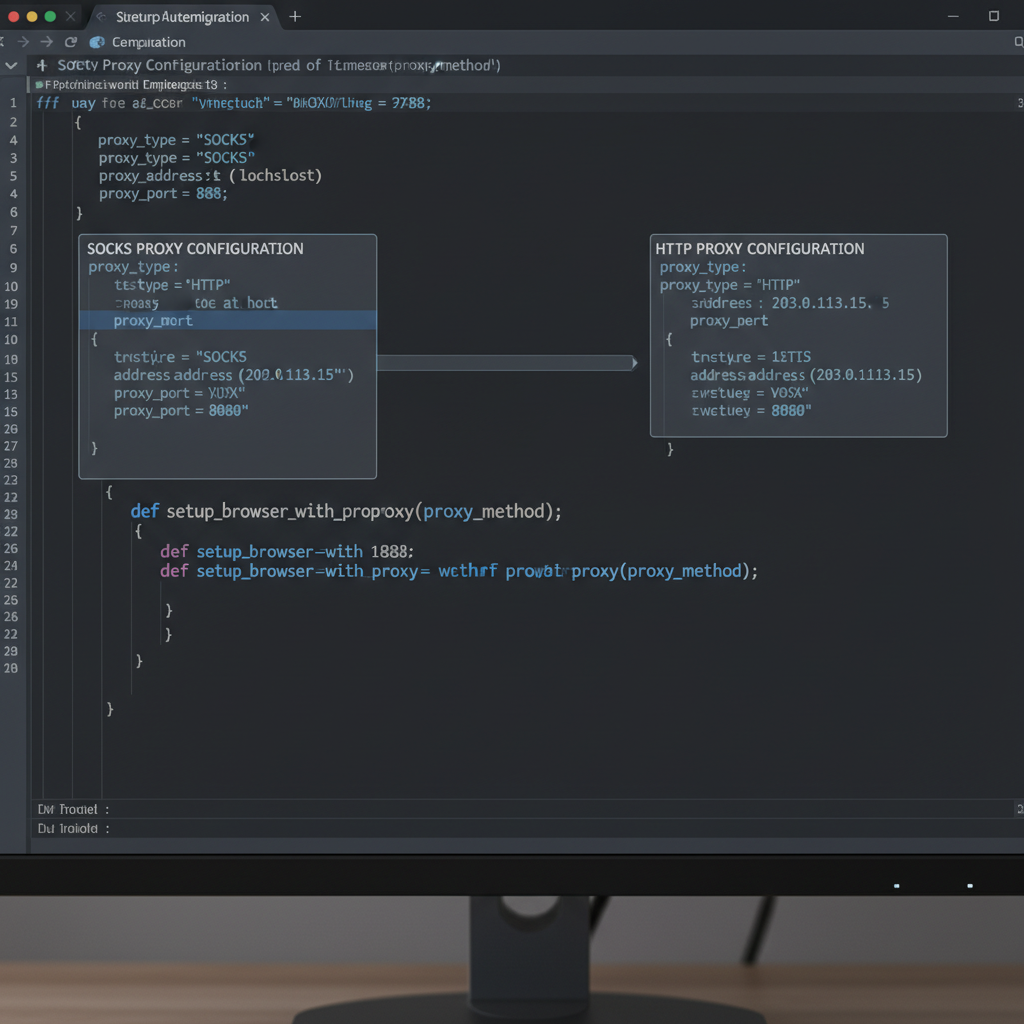
Browser automation integrates proxy protocols through different configuration pathways that affect profile isolation and session persistence. HTTP proxies require 73% less configuration code in browser automation scripts due to native browser support.
Proxy configuration methods vary by protocol and browser engine. HTTP proxies use standard browser proxy settings, PAC file configuration, or command-line arguments. SOCKS implementation requires system proxy configuration, application-specific settings, or custom socket management code.
HTTP proxy browser integration: Configure through browser proxy settings, command-line flags, or WebDriver proxy capabilities. Browser handles connection pooling, authentication, and error recovery automatically. Profile switching requires proxy setting updates without browser restart.
SOCKS proxy browser integration: Configure through system proxy settings, application proxy configuration, or custom proxy management. Requires manual connection handling, authentication management, and error recovery implementation. Profile switching may require browser restart or socket reset.
Authentication flow handling: HTTP proxies participate in browser authentication using standard HTTP auth mechanisms. Browser manages credential storage and retry logic. SOCKS authentication occurs at socket level before browser involvement.
Session persistence impact: HTTP proxies maintain session state through browser cookie management and connection reuse. SOCKS connections create persistent tunnels that may conflict with browser session isolation requirements.
Profile isolation maintenance requires different approaches for each protocol. HTTP proxy configurations isolate through browser profile separation and proxy rotation. SOCKS isolation requires system-level network configuration and socket management that can affect other applications.
Automation script compatibility favors HTTP implementation for cross-platform operations. Selenium, Playwright, and Puppeteer provide built-in HTTP proxy support. SOCKS integration requires additional libraries, error handling, and platform-specific configuration code that increases maintenance overhead.
Anti detect browser cookie management works differently with each protocol. HTTP proxies allow browser-level cookie isolation and sharing controls. SOCKS connections may bypass browser cookie restrictions, creating session leakage between profiles that platforms can detect.
Frequently Asked Questions
Can you switch between SOCKS and HTTP proxies on the same browser profile?
You can switch proxy types, but session state breaks during the transition. Browser profiles maintain connection fingerprints tied to the original proxy protocol. Switching requires profile environment reset.
Do residential proxies work better with SOCKS5 or HTTP protocols?
Residential proxy providers offer both protocols on the same IP pool. HTTP protocol reduces configuration complexity for browser-based operations. SOCKS5 provides better performance for high-throughput automation tasks.
Which proxy type uses more bandwidth for the same browsing activity?
HTTP proxies add 8-12% bandwidth overhead due to header processing and connection reuse limitations. SOCKS5 proxies maintain persistent connections with 3-5% overhead. The difference becomes significant at scale operations.
Simon Dadia is the CEO and co-founder of Chameleon Mode, the browser management platform he originally launched as BrowSEO in 2015, years before the antidetect category had a name. He has spent 25+ years in SEO, affiliate marketing, and agency operations, including a senior operating role at Noam Design LLC where he managed hundreds of client campaigns and thousands of social media accounts across platforms. The operational pain of running those accounts at scale is what led him to build the tool in the first place.
Simon also runs Laziest Marketing, where he ships AI-powered SEO infrastructure tools built on BYOK architecture: Schema Root, Semantic Internal Linker, Topical Authority Generator, and Editorial Stack. Father of 4. Based in Israel.


