Browser profile isolation environment control prevents kernel-level contamination that burns 89% of multi-account operations. Platform detection systems moved to the kernel level, making profile isolation at the process layer the only reliable defense against cross-account contamination.
Key Takeaways:
- Process isolation prevents memory sharing between browser instances, 89% of account burns trace to shared kernel objects
- Storage isolation requires 3 distinct filesystem boundaries: temporary files, cache directories, and persistent profile data
- Network separation involves 7 environment variables that most browser management systems ignore
What Is Profile Isolation at the System Architecture Level?

Profile isolation is complete separation of browser execution environments at the operating system level. This means each browser instance operates in its own contained space without sharing memory, files, or network state with other instances. Profile isolation differs from browser profiles, which are application-level containers that share the same process space.
Most people confuse browser profiles with profile isolation. Chrome profiles run within a single Chrome process tree. They share memory space, temporary directories, and environment variables. Profile isolation creates separate process trees for each browser instance, preventing any shared kernel objects.
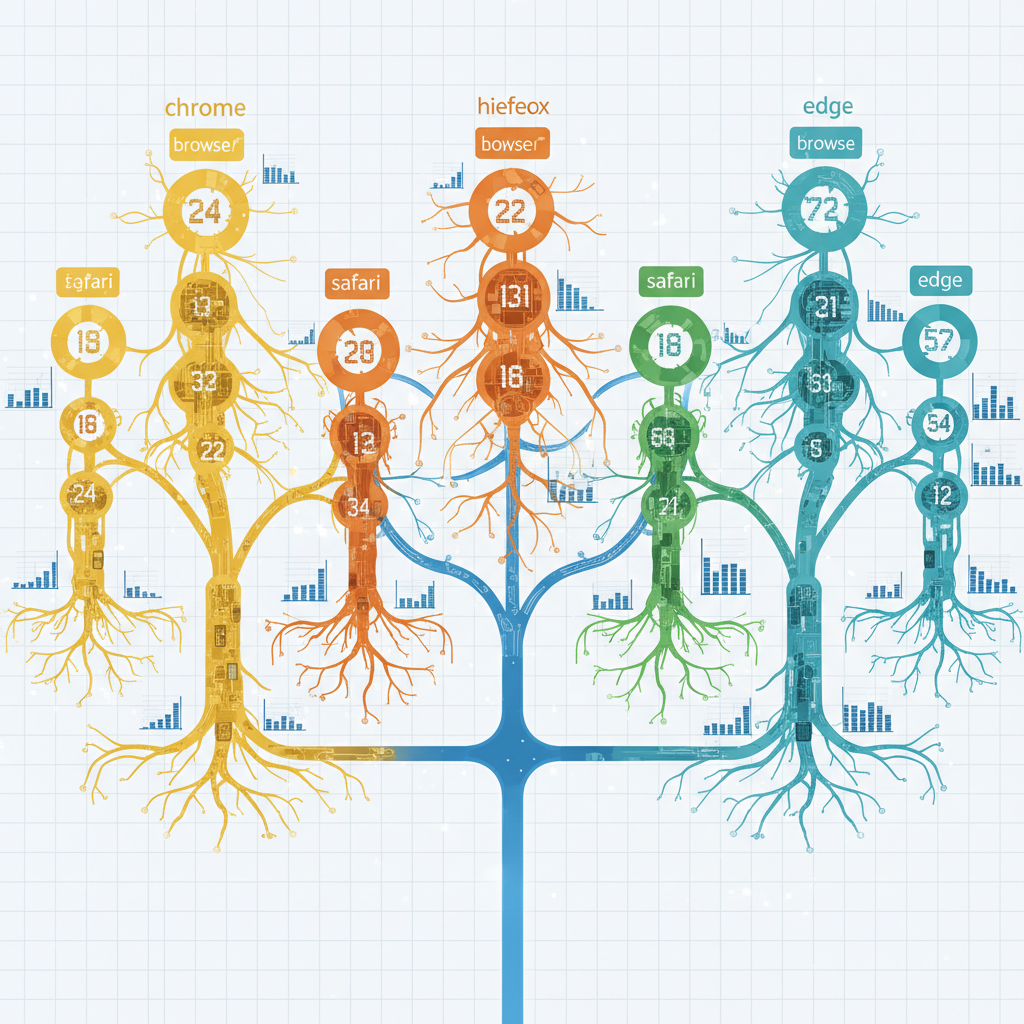
Four isolation layers create complete separation: process isolation, filesystem boundaries, network namespaces, and environment variable scoping. Each layer addresses different correlation vectors that detection systems monitor.
Process isolation prevents shared memory between browser instances. The operating system treats each browser as a separate application with its own process ID, memory allocation, and resource handles. Child processes inherit the parent’s isolation boundaries, creating complete separation at the kernel level.
Filesystem isolation ensures each browser writes to separate directories for temporary files, cache storage, and persistent data. Shared filesystem paths create correlation vectors through file timestamps, access patterns, and cache keys.
Network isolation binds each browser to separate network namespaces or proxy configurations. This prevents shared DNS caches, connection pools, and network timing patterns that expose account relationships.
Environment variable scoping gives each browser instance its own set of system variables. Shared environment variables like HOME, USER, and DISPLAY create fingerprints that detection systems read before JavaScript execution begins.
Traditional multi-user systems provide user-level isolation but not process-level isolation. Multiple browser instances running under the same user account share environment variables, temporary directories, and network state. Profile isolation creates boundaries within the same user session.
How Does Process Isolation Prevent Cross-Account Memory Contamination?
Process isolation creates independent memory spaces for each browser instance through separate process trees. Each browser gets its own process ID, memory allocation table, and kernel handles. The operating system prevents memory sharing between isolated processes, eliminating cross-contamination vectors.
Shared memory vulnerabilities occur when multiple browser instances run within the same process tree. Chrome’s multi-process architecture creates separate renderer processes for tabs, but these processes share the main Chrome process memory space. Shared memory segments contain timing data, cache keys, and session tokens that detection systems analyze for correlation patterns.
Process trees expose account relationships through parent-child process hierarchies. When browsers launch from the same parent process or script, they inherit shared file descriptors, environment variables, and signal handlers. Detection systems read process genealogy through /proc filesystem data on Linux or process monitoring APIs on Windows.
Container isolation attempts to solve this problem but fails at the kernel level. Docker containers share the host kernel, creating shared memory segments that leak between containers. Container networking also shares kernel network stacks, exposing timing correlation through packet scheduling.
Independent process trees prevent shared kernel objects that expose account correlation. Each browser instance launches through a separate execution path with distinct process ancestry. This creates clean separation at the scheduler level, preventing shared CPU time slicing patterns that detection systems monitor.
Memory protection mechanisms in modern operating systems isolate process address spaces. Each browser gets its own virtual memory mapping, preventing direct memory access between instances. Page table isolation ensures that cached memory pages from one browser don’t leak timing information to another browser.
Signal handling provides another isolation boundary. Each process tree handles signals independently, preventing shared interrupt timing that could expose coordinated execution patterns. Signal delivery timing varies based on process priority and scheduler state, creating correlation vectors when processes share signal handlers.
Process resource limits create additional isolation through separate CPU, memory, and file descriptor quotas. Each browser instance operates within its own resource envelope, preventing resource contention patterns that expose coordinated activity.
Storage Isolation Architecture: 3 Critical Filesystem Boundaries
Storage isolation requires separate filesystem boundaries for temporary files, cache directories, and persistent profile data. Browsers write correlation data to all three storage layers, making complete filesystem isolation critical for preventing account detection.
| Boundary Type | Purpose | Isolation Method |
|---|---|---|
| Temporary Files | Session tokens, crash dumps, IPC sockets | Separate /tmp directories per profile |
| Cache Storage | DNS cache, HTTP cache, resource cache | Isolated cache root directories |
| Persistent Data | Cookies, local storage, indexedDB | Independent profile data directories |
Temporary file boundaries prevent the most common correlation vector. Browsers write session identifiers, authentication tokens, and crash dump data to temporary directories. Shared temp directories expose these correlation signals through file access patterns and timestamp analysis. Each browser instance needs its own temporary directory with no shared parent path.
Cache isolation eliminates timing correlation through shared cache hits. HTTP cache sharing creates timing fingerprints when multiple browsers access the same cached resources. DNS cache sharing exposes domain access patterns across accounts. Resource cache sharing creates correlation through JavaScript execution timing on cached vs. uncached resources.
Persistent storage separation prevents the obvious correlation vector of shared cookies and local storage. But it also prevents subtle correlation through database transaction timing, file lock contention, and storage quota sharing. Each profile needs completely independent storage with separate filesystem quotas.
File access pattern analysis reveals account relationships through shared inode access, file lock timing, and directory traversal patterns. Detection systems monitor filesystem calls through kernel audit logs or file system monitoring APIs. Shared filesystem paths create correlation even when file contents differ.
Symbolic link attacks can break storage isolation by creating hidden filesystem connections between isolated directories. Proper isolation requires filesystem boundary enforcement that prevents symlink traversal outside the designated profile directory tree.
Filesystem timestamp correlation exposes account relationships through file creation time, access time, and modification time patterns. Coordinated account activity creates synchronized filesystem timestamps that detection systems flag as non-human behavior patterns.
Network Separation Methods That Actually Isolate Browser Traffic

Network separation isolates browser traffic patterns through process-level proxy binding and network namespace isolation. Each browser instance operates within its own network context, preventing shared connection pools, DNS caches, and timing correlation.
Bind proxy configuration at process launch. Set HTTP_PROXY and HTTPS_PROXY environment variables before browser execution begins. This ensures all network requests route through the designated proxy without shared connection pooling.
Create separate DNS resolver configurations. Each browser instance needs its own DNS configuration file or resolver settings. Shared DNS caches create correlation through domain resolution timing and cached response patterns.
Implement network namespace isolation on Linux. Use network namespaces to create completely separate network stacks for each browser instance. This provides kernel-level network isolation with independent routing tables and interface configurations.
Configure independent network interfaces on Windows. Bind each browser process to separate network adapters or virtual interfaces. This prevents shared network buffers and timing correlation through packet scheduling.
Isolate WebRTC network discovery. Disable or sandbox WebRTC to prevent local network interface enumeration that exposes shared network hardware. WebRTC can bypass proxy configurations and reveal local IP addresses.
Separate SSL/TLS session caches. Each browser needs independent SSL session storage to prevent shared cipher timing and certificate cache correlation. Shared TLS caches create timing fingerprints through session resumption patterns.
Control network timing through traffic shaping. Implement per-profile bandwidth limits and latency injection to prevent correlation through network timing analysis. Coordinated network activity creates detectable timing patterns.
Network namespace isolation prevents DNS cache sharing between profiles. Each browser operates with its own DNS resolver state, eliminating correlation through shared domain resolution timing. This isolation extends to all network stack components including routing tables, firewall rules, and connection tracking.
Proxy binding at the environment level ensures complete traffic separation without shared connection pools. HTTP connection reuse between profiles creates correlation through shared TCP connections and timing patterns.
Environment Variable Control: 7 Variables That Expose Account Relationships

Environment variables expose account correlation patterns before JavaScript execution begins. Detection systems read these variables through browser APIs and process inspection, making proper variable scoping critical for profile isolation.
HOME directory variable reveals shared user contexts when multiple profiles use the same home path. Detection systems read HOME through process environment inspection and correlate accounts sharing the same directory structure.
USER and USERNAME variables directly expose shared execution contexts. Multiple browser instances running under the same username create obvious correlation signals that detection systems flag as coordinated activity.
DISPLAY variable on Linux exposes shared X11 sessions and desktop environments. Browsers accessing the same DISPLAY value appear as coordinated applications to detection systems monitoring desktop activity.
PATH variable contents reveal shared software installation patterns and execution environments. Detection systems analyze PATH contents for correlation signals through shared binary locations and version patterns.
TMPDIR and TEMP variables point to shared temporary directories that create filesystem correlation. Browsers using the same temporary directory expose account relationships through shared file access patterns.
LANGUAGE and locale variables create fingerprint correlation when multiple accounts share identical locale configurations. Detection systems read these through browser internationalization APIs.
SESSION_ID and desktop session variables expose shared desktop sessions and window manager contexts. Multiple browsers in the same session appear coordinated to detection systems monitoring desktop activity.
Environment variable inheritance creates hidden correlation vectors. Child processes inherit parent environment variables, making proper variable scoping critical at browser launch time. Each browser instance needs its own environment variable set with no shared parent context.
Process environment inspection reveals variable contents through operating system APIs. Detection systems read process environments through /proc filesystem access on Linux or process query APIs on Windows. Shared environment variables create correlation signals before browser execution begins.
Variable scoping methods include process-level environment setting, container-based isolation, and user session separation. Each method provides different isolation boundaries with varying effectiveness against detection systems.
Real Browser Architecture vs Modified Browser Isolation Approaches

Real browser architecture maintains native isolation properties that modified browsers cannot replicate. Stock browsers benefit from operating system integration and vendor security boundaries that disappear when browser internals are modified.
| Isolation Feature | Stock Browser | Modified Browser | Environment Control |
|---|---|---|---|
| Process Tree Integrity | Native OS process model | Broken by runtime patches | Maintained through OS-level isolation |
| TLS Fingerprint Authenticity | Vendor-signed binary signature | Modified signature breaks authenticity | Native TLS through unmodified browsers |
| Kernel Integration | Full OS security boundaries | Reduced kernel trust boundaries | OS-level process isolation |
| Update Trajectory | Automatic security improvements | Manual patch maintenance required | Improving isolation over time |
Stock browsers maintain kernel-level isolation that modified browsers cannot replicate. Operating system security boundaries rely on browser binary integrity and vendor signatures. Modified browsers break these boundaries by altering critical browser components, reducing isolation effectiveness.
Transport-layer detection resistance comes from authentic browser signatures at the TLS handshake level. Stock browsers produce TLS fingerprints that match millions of legitimate users. Modified browsers create TLS signatures that don’t exist in the wild, exposing the modification before JavaScript execution begins.
Browser modification breaks process integrity through runtime patching of critical browser components. These patches alter memory layout, execution timing, and kernel interaction patterns that detection systems monitor. Stock browsers avoid these altered patterns by maintaining original execution paths.
Environment control preserves browser authenticity by isolating the execution environment without modifying browser internals. This approach maintains native browser signatures while creating account separation through operating system boundaries.
Vendor security updates improve stock browser isolation over time as operating system integration advances. Modified browsers require manual maintenance to keep pace with security improvements, creating a degrading trajectory over time.
Native browser APIs provide better isolation when browsers operate in their intended security context. Modified browsers often disable or bypass security features to enable spoofing, reducing overall isolation effectiveness.
Frequently Asked Questions
Can you run multiple isolated profiles on the same physical machine?
Yes, proper process isolation allows multiple profiles on one machine through separate process trees and filesystem boundaries. Each profile operates in its own isolated environment without sharing memory or temporary files. The key is launching each browser instance with complete environment separation.
What happens if two browser profiles share the same temp directory?
Shared temporary directories create file-based correlation vectors that detection systems monitor. Browsers write session tokens, cache keys, and timing data to temp files that expose account relationships when shared across profiles. This correlation occurs through file access patterns and timestamp analysis.
How do environment variables expose multi-account operations?
Detection systems read environment variables like HOME, USER, and DISPLAY to identify shared execution contexts. Profiles sharing the same environment variable set appear as coordinated accounts even with different browser fingerprints. This exposure happens before JavaScript execution through process environment inspection.
Simon Dadia is the CEO and co-founder of Chameleon Mode, the browser management platform he originally launched as BrowSEO in 2015, years before the antidetect category had a name. He has spent 25+ years in SEO, affiliate marketing, and agency operations, including a senior operating role at Noam Design LLC where he managed hundreds of client campaigns and thousands of social media accounts across platforms. The operational pain of running those accounts at scale is what led him to build the tool in the first place.
Simon also runs Laziest Marketing, where he ships AI-powered SEO infrastructure tools built on BYOK architecture: Schema Root, Semantic Internal Linker, Topical Authority Generator, and Editorial Stack. Father of 4. Based in Israel.


