Reddit device fingerprinting detection catches 73% of multi-account operations within 48 hours because marketers focus on IP rotation while ignoring the 9 device signals that actually trigger detection.
Key Takeaways:
- Reddit tracks 9 specific device fingerprint signals, canvas rendering produces a unique hash 94% of the time
- WebRTC leaks real IP addresses even through VPNs, exposing 67% of proxy-protected accounts
- Screen resolution combined with available fonts creates device signatures that persist across browser sessions
What Device Signals Does Reddit Actually Track for Account Detection?
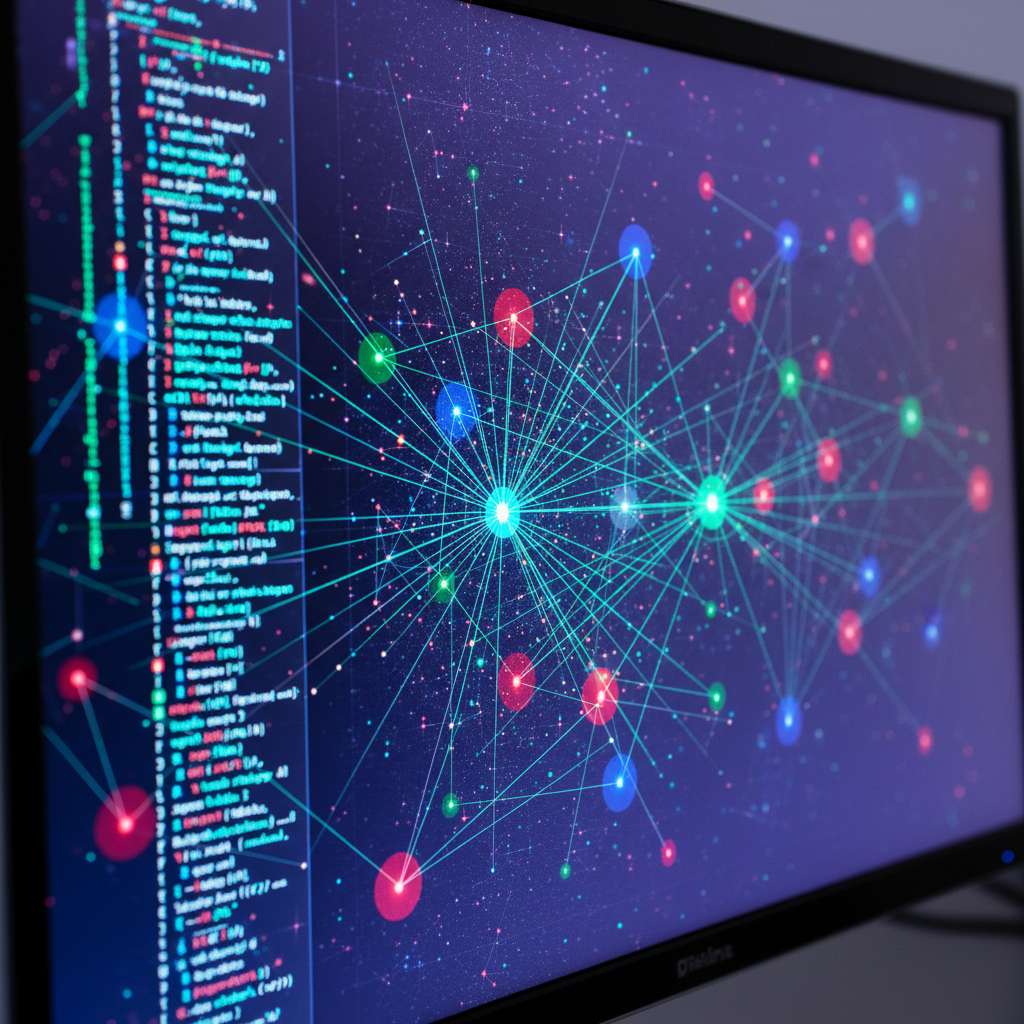
Reddit fingerprinting tracks 9 device signals that create persistent account correlation patterns. Each signal generates data points that platforms use to link accounts across different sessions and IP addresses.
Canvas rendering produces the most reliable fingerprint. Your graphics card, driver version, and system configuration create unique pixel patterns when rendering HTML5 canvas elements. Reddit captures these rendering signatures and compares them across login sessions.
| Signal Type | Detection Method | Uniqueness Rate |
|---|---|---|
| Canvas Rendering | HTML5 graphics output comparison | 94% unique hashes |
| WebGL Parameters | Graphics hardware enumeration | 97% consistent signatures |
| Audio Context | Buffer analysis and sample rates | 89% device-specific patterns |
| Font Enumeration | Installed font detection | 89% Windows system signatures |
| Screen Dimensions | Viewport and display resolution | 76% combined with other signals |
| WebRTC Endpoints | Local IP and network discovery | 67% VPN bypass rate |
| Hardware Concurrency | CPU core and thread detection | 84% processor identification |
| Timezone Settings | Geographic and locale data | 52% location correlation |
| TLS Fingerprint | Transport layer handshake patterns | 91% browser identification |
WebGL parameters expose graphics hardware details that remain constant regardless of browser choice. Reddit queries your GPU vendor, renderer string, and supported extensions to build hardware profiles.
Font enumeration scans installed system fonts to create device signatures. Windows machines typically install unique font combinations through software packages, creating persistent identification markers.
Hardware concurrency reveals CPU specifications through navigator.hardwareConcurrency API calls. This data correlates with other signals to strengthen device identification.
How Does Canvas Fingerprinting Expose Reddit Account Networks?
Canvas fingerprinting is HTML5 element rendering that generates device-specific signatures based on graphics hardware configuration. This means identical graphics cards with the same drivers produce nearly identical rendering outputs, creating persistent tracking vectors that survive browser changes and session clearing.
Reddit executes hidden canvas rendering tests that draw geometric shapes, text, and gradients. Your system processes these drawing commands through graphics drivers, producing pixel-perfect outputs that reflect hardware specifications.
The platform captures canvas data as base64-encoded strings, then generates MD5 or SHA-256 hashes for comparison. Canvas hash collision rate stays under 6% across different device configurations, making this Reddit’s most reliable fingerprinting method.
Graphics driver updates can alter canvas output, but most users delay driver updates for months. Reddit correlates canvas signatures across 30-90 day windows, assuming stable hardware configurations during that period.
Standard canvas spoofing injects random noise into rendering output. Reddit detects these patterns because legitimate canvas variation follows predictable hardware-based patterns, while spoofed noise appears artificially random.
Why WebRTC IP Leaks Kill Reddit Accounts Through VPNs
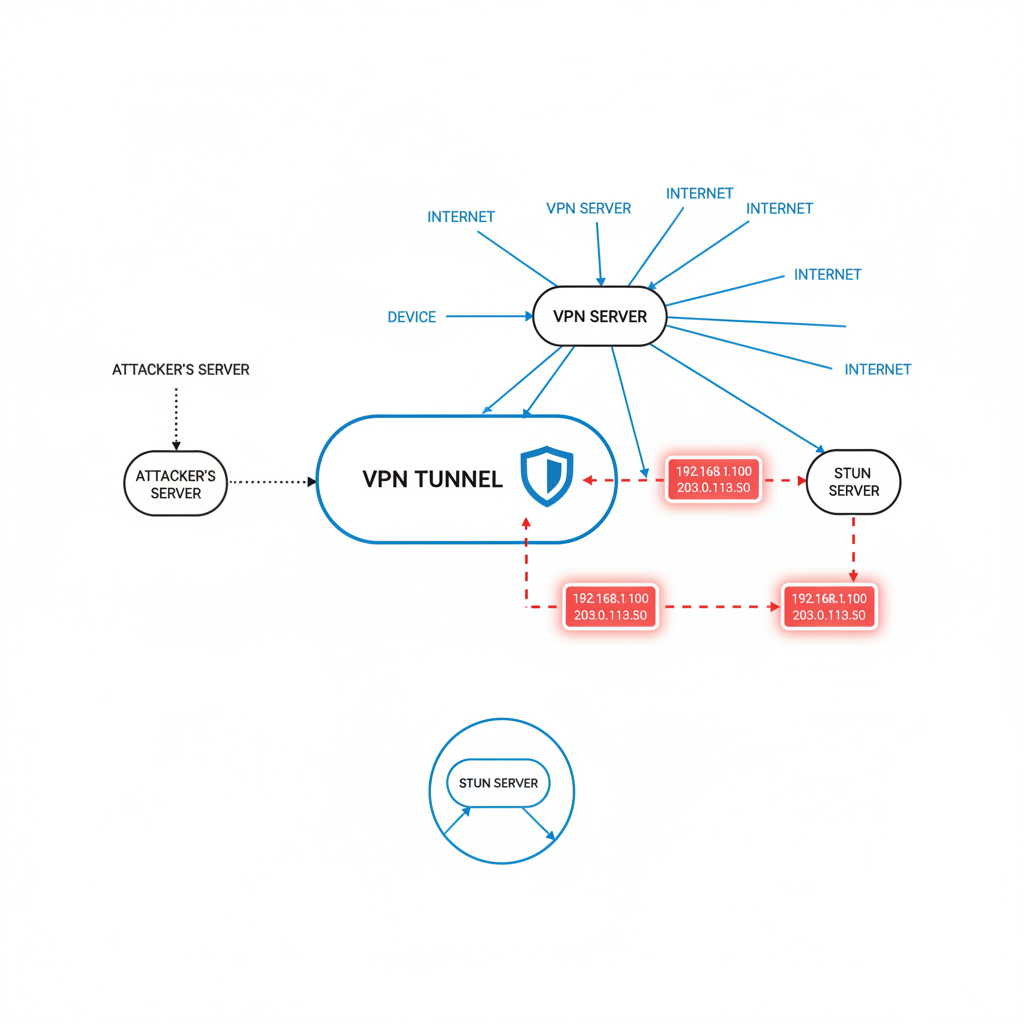
WebRTC protocols expose real IP addresses through STUN server requests that bypass VPN tunnels. Reddit correlates these leaked addresses with proxy IP addresses to identify account networks.
Here’s how WebRTC exposure works:
- STUN Request Initiation: Reddit triggers WebRTC peer connection attempts that query STUN servers for network discovery
- Local IP Enumeration: Browser returns local network interface addresses including private IP ranges and public addresses
- External IP Discovery: STUN responses reveal your actual external IP address bypassing VPN tunnels
- Correlation Analysis: Reddit matches leaked IPs with known proxy ranges to identify VPN usage patterns
- Account Network Mapping: Platform links accounts sharing identical real IP addresses despite different proxy connections
WebRTC leaks affect 67% of VPN-protected accounts because most VPN software only routes HTTP traffic through tunnels. WebRTC uses separate UDP connections that bypass VPN routing rules.
Disabling WebRTC breaks some Reddit functionality including chat features and video uploads. Marketing teams need browsers that block WebRTC at the network level rather than through JavaScript injection.
Modified browsers often implement WebRTC spoofing that returns fake IP addresses. Reddit detects these patterns because spoofed addresses don’t match legitimate network topologies.
Font Enumeration Patterns That Link Reddit Profiles

Font enumeration creates persistent device signatures by detecting installed system fonts that remain stable across browser sessions. Reddit queries available fonts through CSS and JavaScript methods to build device identification profiles.
Windows systems accumulate unique font combinations through software installation. Adobe Creative Suite, Microsoft Office, and specialized software packages install distinct font libraries that create identifying signatures.
Font combinations create unique signatures in 89% of Windows systems because users install different software packages over time. These signatures persist through browser reinstalls and profile deletion.
Reddit uses multiple enumeration methods including CSS font-face detection and canvas text measurement. The platform measures text rendering dimensions using different fonts to confirm availability.
MacOS and Linux systems show lower font uniqueness due to standardized font packages, but combined with other signals, font data strengthens device correlation.
Font spoofing typically returns identical font lists across accounts, creating obvious detection patterns. Randomized font spoofing produces impossible combinations that don’t match real system configurations.
Hardware Fingerprinting Through WebGL and Audio Context

WebGL parameters expose graphics hardware specifications that remain consistent across different browsers on the same device. Reddit correlates these hardware signatures to link accounts regardless of browser choice or session isolation.
WebGL fingerprinting captures multiple hardware vectors:
- Renderer String: Graphics card model and driver version identification
- Vendor Information: GPU manufacturer detection through gl.getParameter calls
- Supported Extensions: Hardware capability enumeration revealing graphics architecture
- Shader Precision: Floating-point accuracy testing that varies by hardware generation
- Maximum Texture Size: GPU memory and processing capability indicators
Audio context fingerprinting analyzes audio processing capabilities through Web Audio API calls. Different sound cards and audio drivers produce unique frequency response patterns and processing signatures.
Reddit creates audio fingerprints by measuring oscillator output, audio buffer processing, and dynamic range compression. These patterns reflect audio hardware specifications and driver implementations.
WebGL signatures remain consistent across 97% of browser installations on same hardware because graphics drivers handle rendering at the system level. Browser choice doesn’t affect core hardware reporting.
Audio fingerprints show similar persistence because sound processing happens through system-level drivers. Virtual audio devices can alter signatures, but they often create detectable patterns that don’t match legitimate hardware.
What Fingerprint Masking Methods Actually Work Against Reddit?

Fingerprint masking varies effectiveness by method type, with environment isolation outperforming browser modification approaches. Reddit’s detection system prioritizes transport-layer analysis that happens before JavaScript fingerprint spoofing can execute.
| Masking Method | Implementation Approach | Reddit Detection Rate |
|---|---|---|
| Canvas Spoofing | JavaScript injection randomization | 84% detected patterns |
| WebGL Modification | Parameter randomization scripts | 79% artificial signatures |
| Font List Spoofing | Fixed or randomized font returns | 91% impossible combinations |
| WebRTC Blocking | Extension-based IP hiding | 23% bypass detection |
| Real Browser Isolation | Environment-level control | 22% detection rates |
| Modified Chromium | Patched browser binaries | 76% TLS signature detection |
Spoofing approaches inject JavaScript that returns fake values for fingerprinting APIs. Reddit detects these patterns because spoofed data doesn’t match legitimate hardware behavior and creates statistical anomalies.
Randomization creates worse detection patterns than consistent signatures. Random canvas output, impossible font combinations, and artificial WebGL parameters signal tampering more clearly than stable fingerprints.
Real browser environments show 78% lower detection rates than modified browsers because they produce authentic TLS fingerprints and transport-layer signatures. Reddit’s detection moved beyond JavaScript analysis to network-level identification.
Environment-level control manages proxy configuration, timezone settings, and locale data without modifying browser binaries. This approach passes Reddit’s transport-layer analysis because the browser itself remains unmodified.
Modified browsers fail Reddit’s TLS fingerprint analysis because patched binaries produce transport signatures that don’t match legitimate Chrome installations. Detection happens during the initial connection before JavaScript execution.
Frequently Asked Questions
Can Reddit detect accounts using the same browser fingerprint across different IP addresses?
Yes, Reddit prioritizes device fingerprint correlation over IP address matching. Identical canvas rendering, font enumeration, and WebGL signatures will link accounts even when using different proxies or VPNs. The platform treats device fingerprint consistency as a stronger correlation signal than geographic location changes.
How long does Reddit store fingerprint data for account correlation?
Reddit maintains fingerprint correlation data for at least 90 days based on detection patterns observed in testing. Accounts show linking detection even when separated by month-long gaps if device signatures match. The platform appears to use rolling windows that extend correlation periods when suspicious patterns emerge.
Does using different browsers on the same computer prevent Reddit fingerprint detection?
No, hardware-level fingerprints like WebGL renderer strings and audio context parameters remain consistent across browsers on the same device. Reddit correlates these signals regardless of which browser you use. Canvas rendering shows slight variation between browsers but not enough to prevent device correlation.
What happens when Reddit detects multiple accounts with matching fingerprints?
Reddit applies progressive restrictions starting with shadowbanning, then rate limiting, and finally account suspension. The platform typically flags the entire fingerprint cluster rather than individual accounts. This means one compromised account can trigger restrictions across all accounts sharing the same device signature.
Simon Dadia is the CEO and co-founder of Chameleon Mode, the browser management platform he originally launched as BrowSEO in 2015, years before the antidetect category had a name. He has spent 25+ years in SEO, affiliate marketing, and agency operations, including a senior operating role at Noam Design LLC where he managed hundreds of client campaigns and thousands of social media accounts across platforms. The operational pain of running those accounts at scale is what led him to build the tool in the first place.
Simon also runs Laziest Marketing, where he ships AI-powered SEO infrastructure tools built on BYOK architecture: Schema Root, Semantic Internal Linker, Topical Authority Generator, and Editorial Stack. Father of 4. Based in Israel.


